CENTCOM's Twitter, YouTube Feeds Hacked by ISIS Supporters

WASHINGTON — The Twitter and YouTube accounts of US Central Command were hacked Monday by people claiming to be sympathizers to the Islamic State militant group, commonly referred to as ISIS.
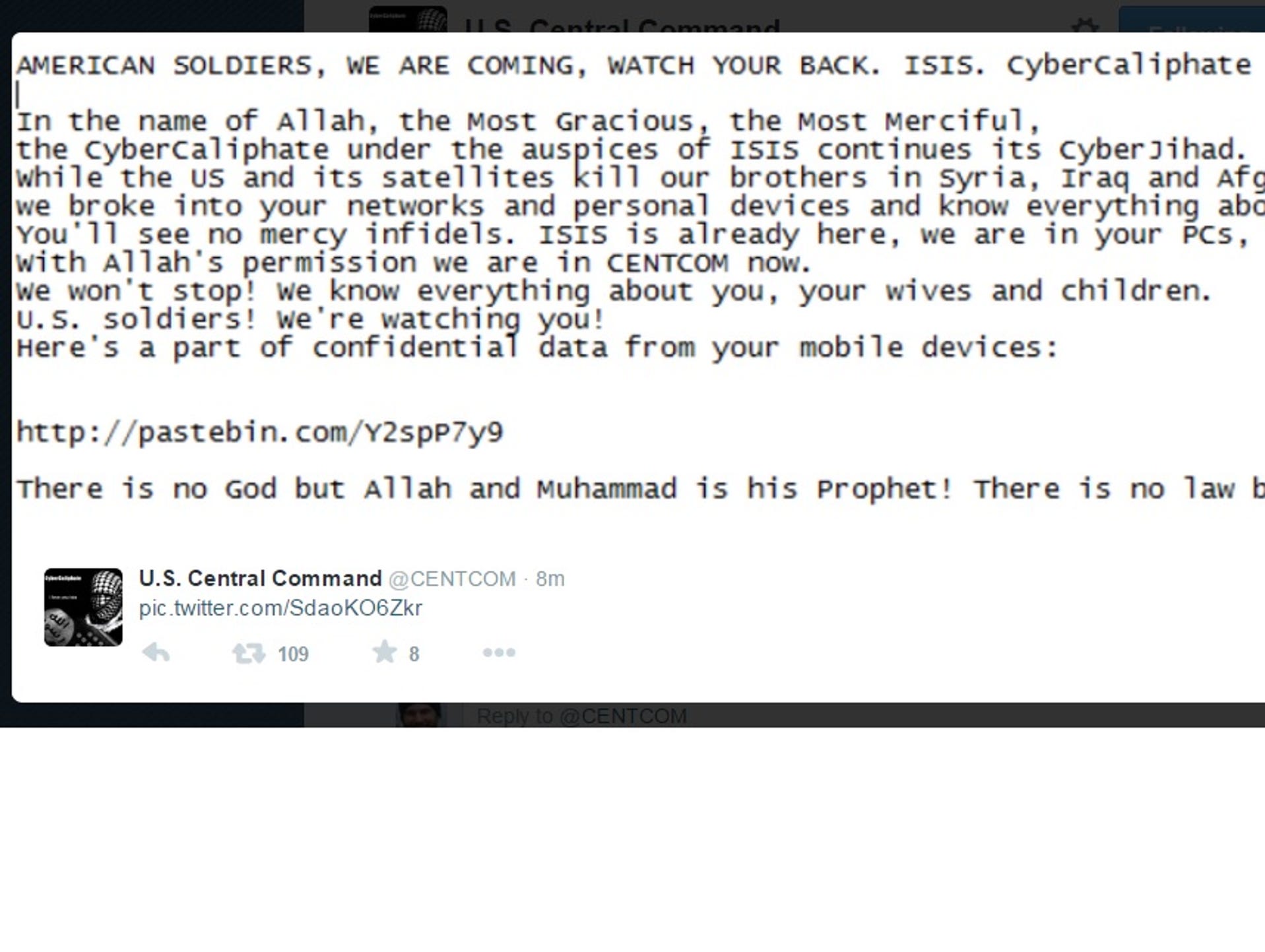
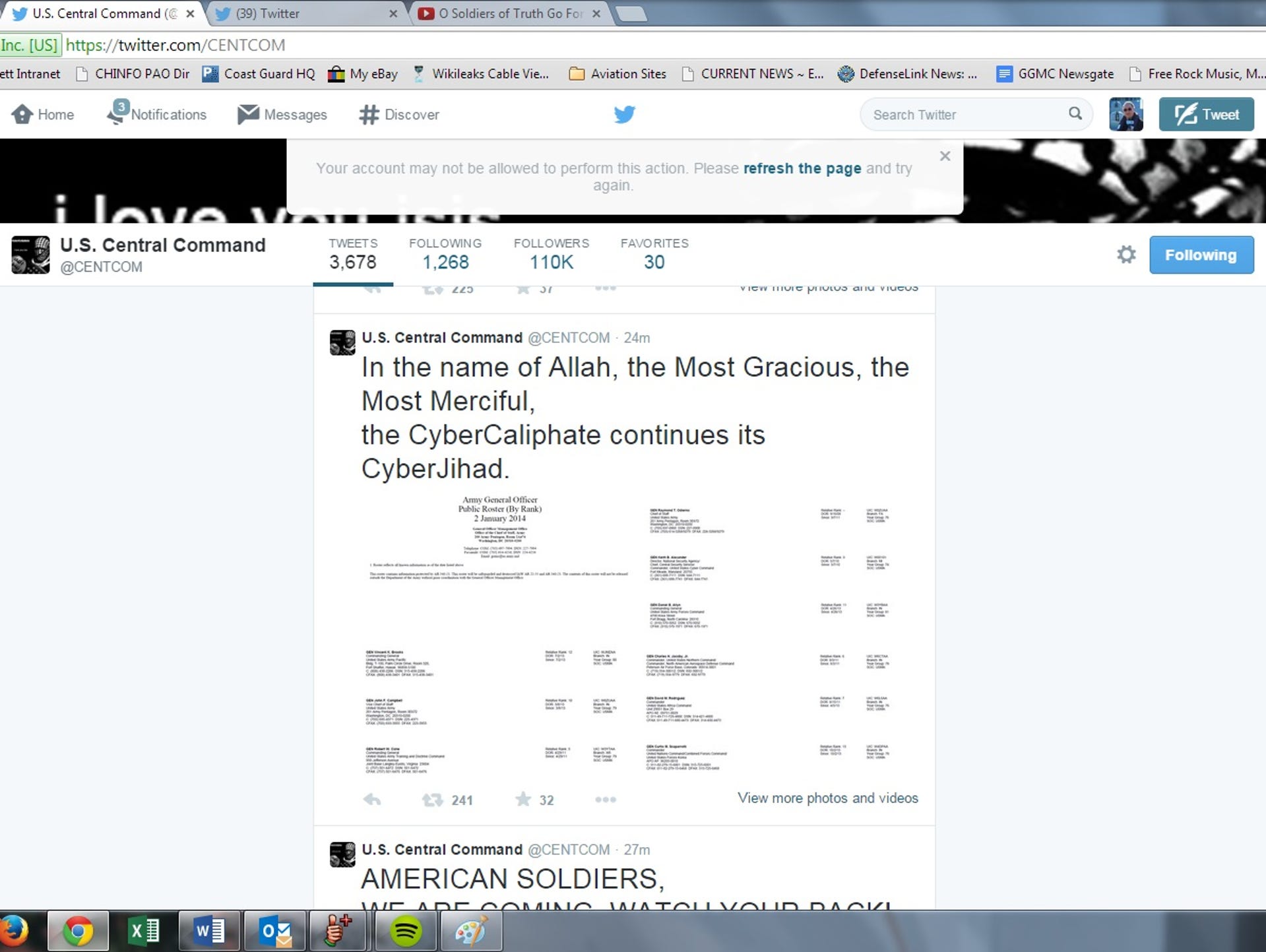
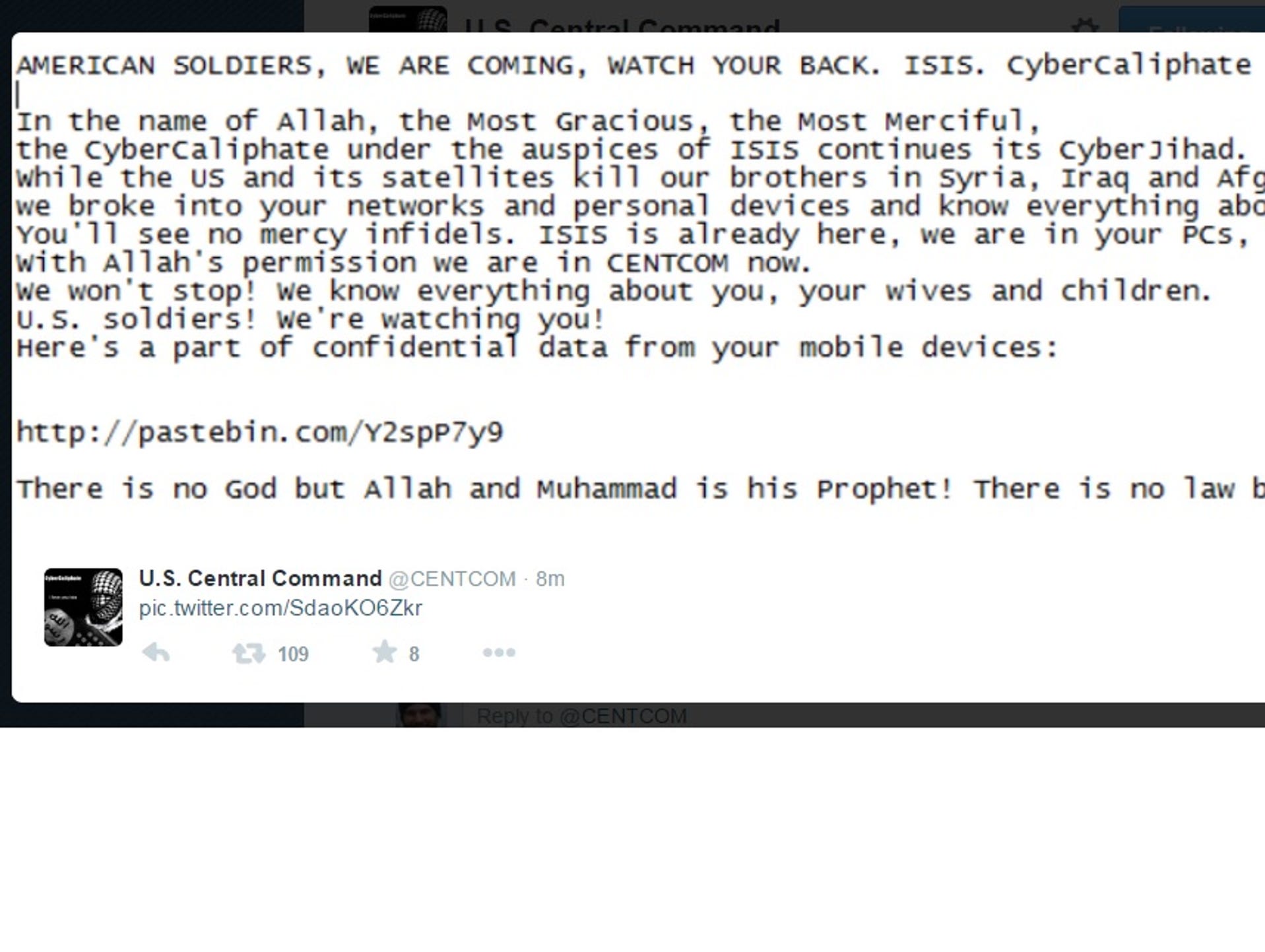
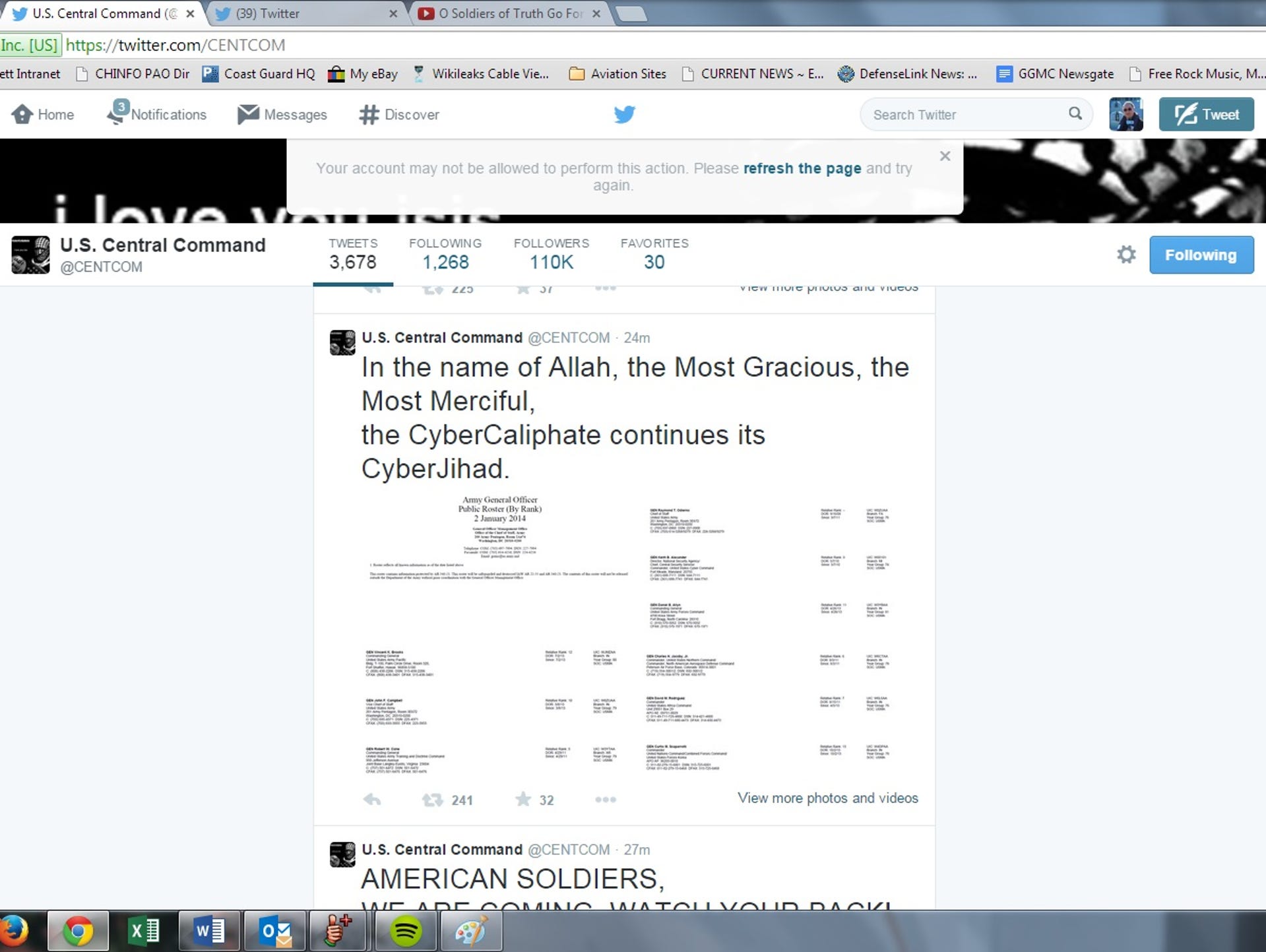
Just after noon East Coast time, the banner image on the @CENTCOM Twitter account shifted to an image of an ISIS fighter with "CyberCaliphate" written next to it. A link was tweeted to a message declaring "AMERICAN SOLDIERS, WE ARE COMING, WATCH YOUR BACK."
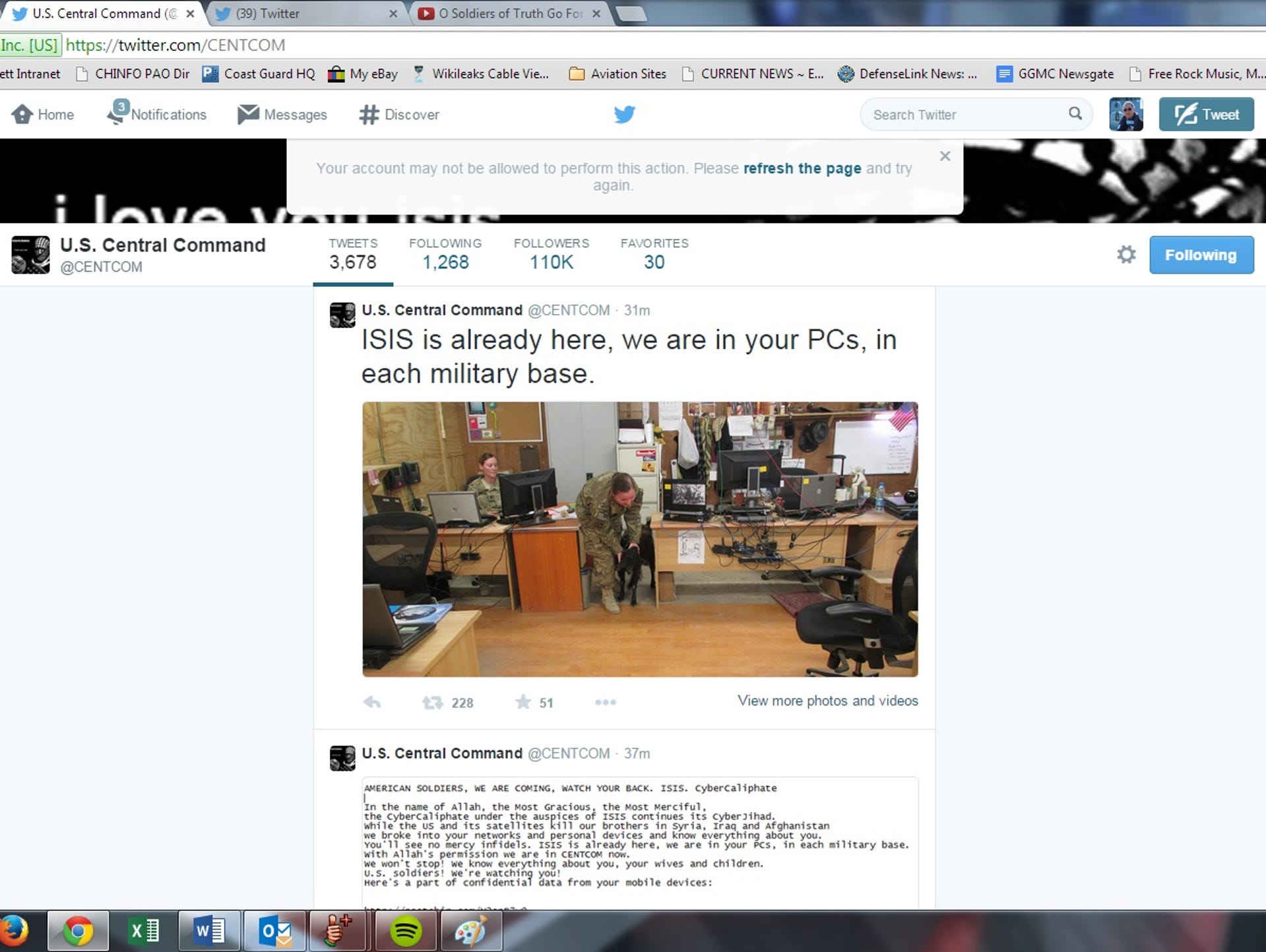
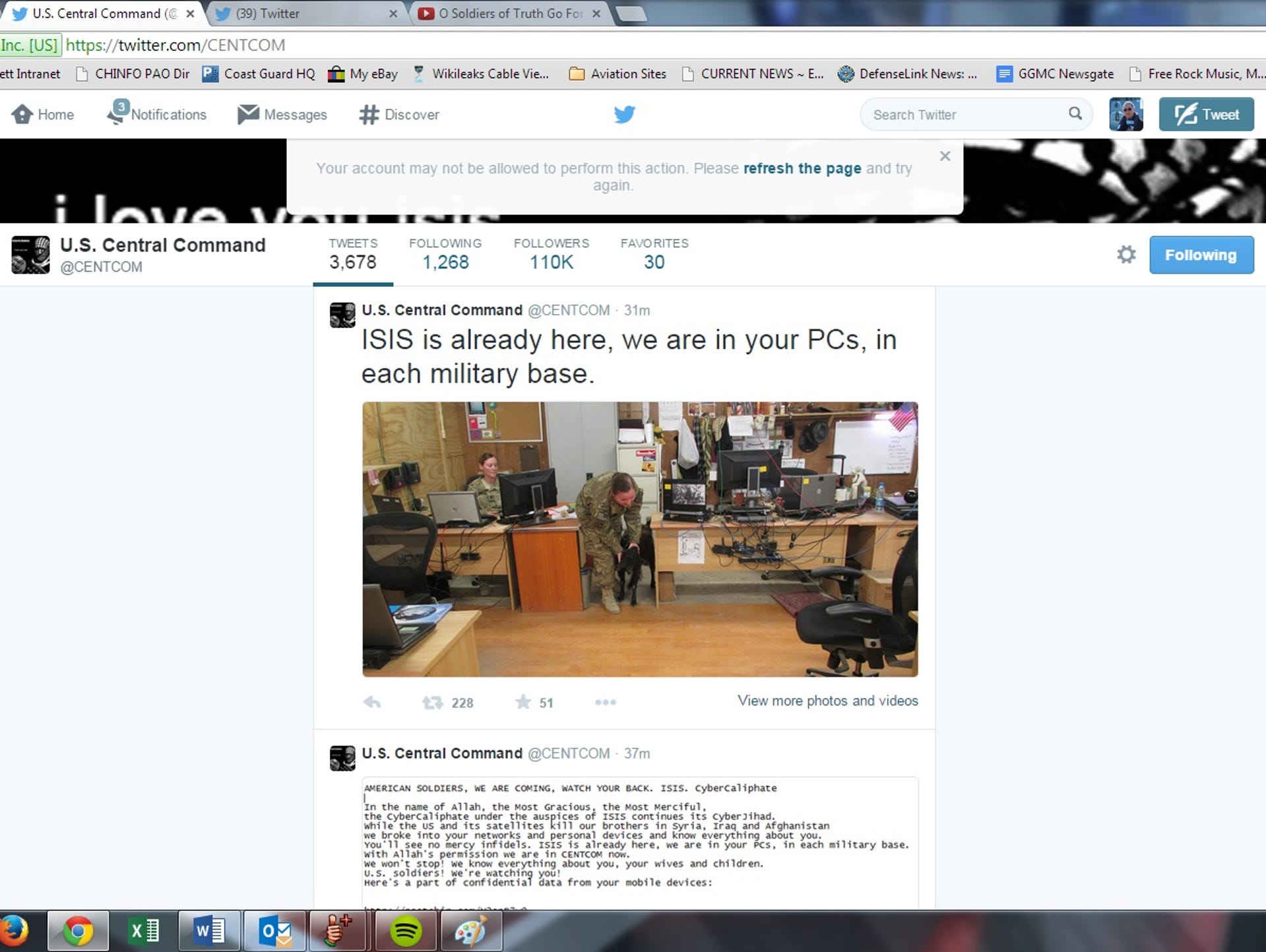
"While the US and its satellites kill our brothers in Syria, Iraq and Afghanistan we broke into your networks and personal devices and know everything about you," the statement read. "You'll see no mercy infidels. ISIS is already here, we are in your PCs, in each military base."
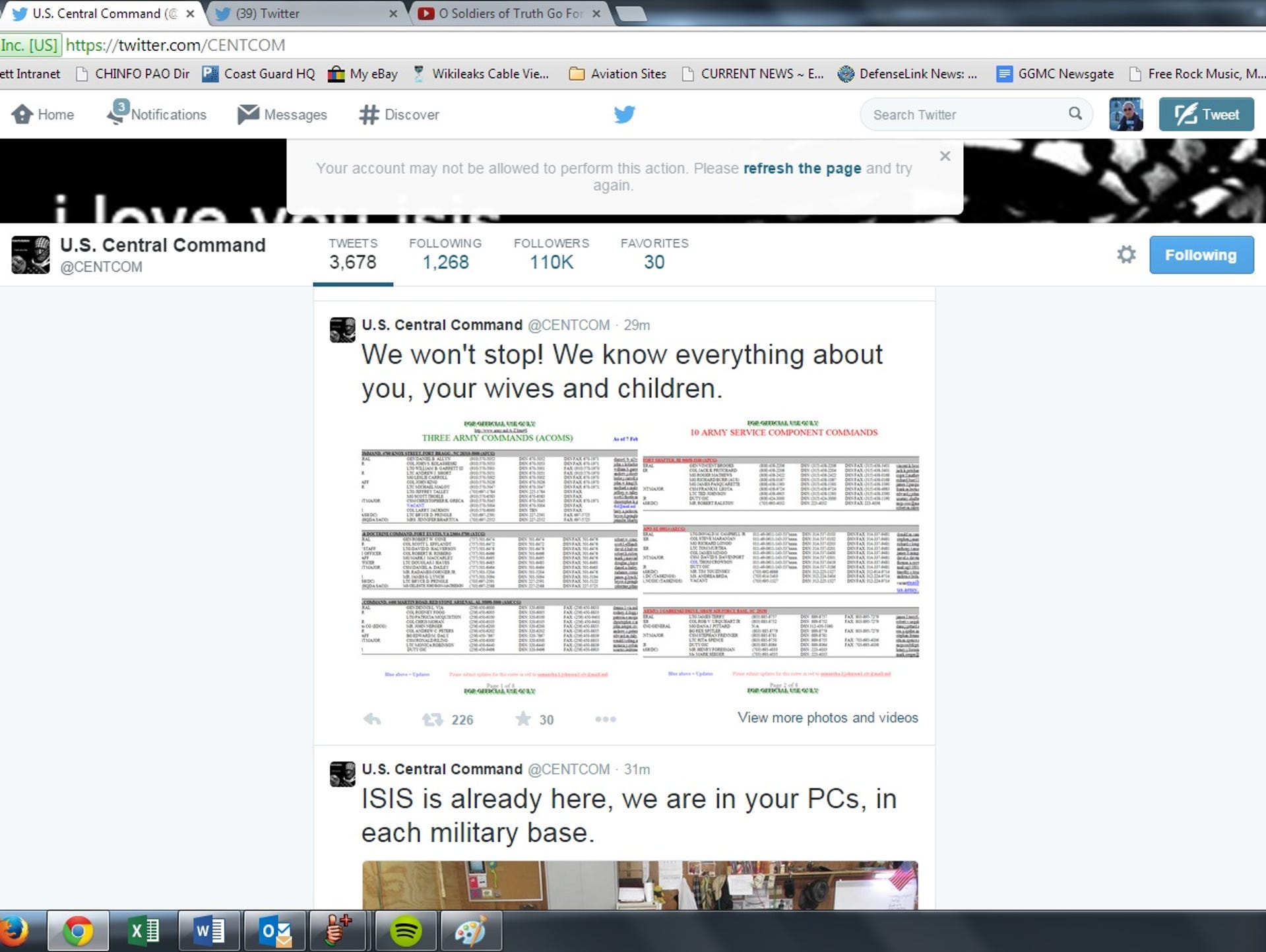
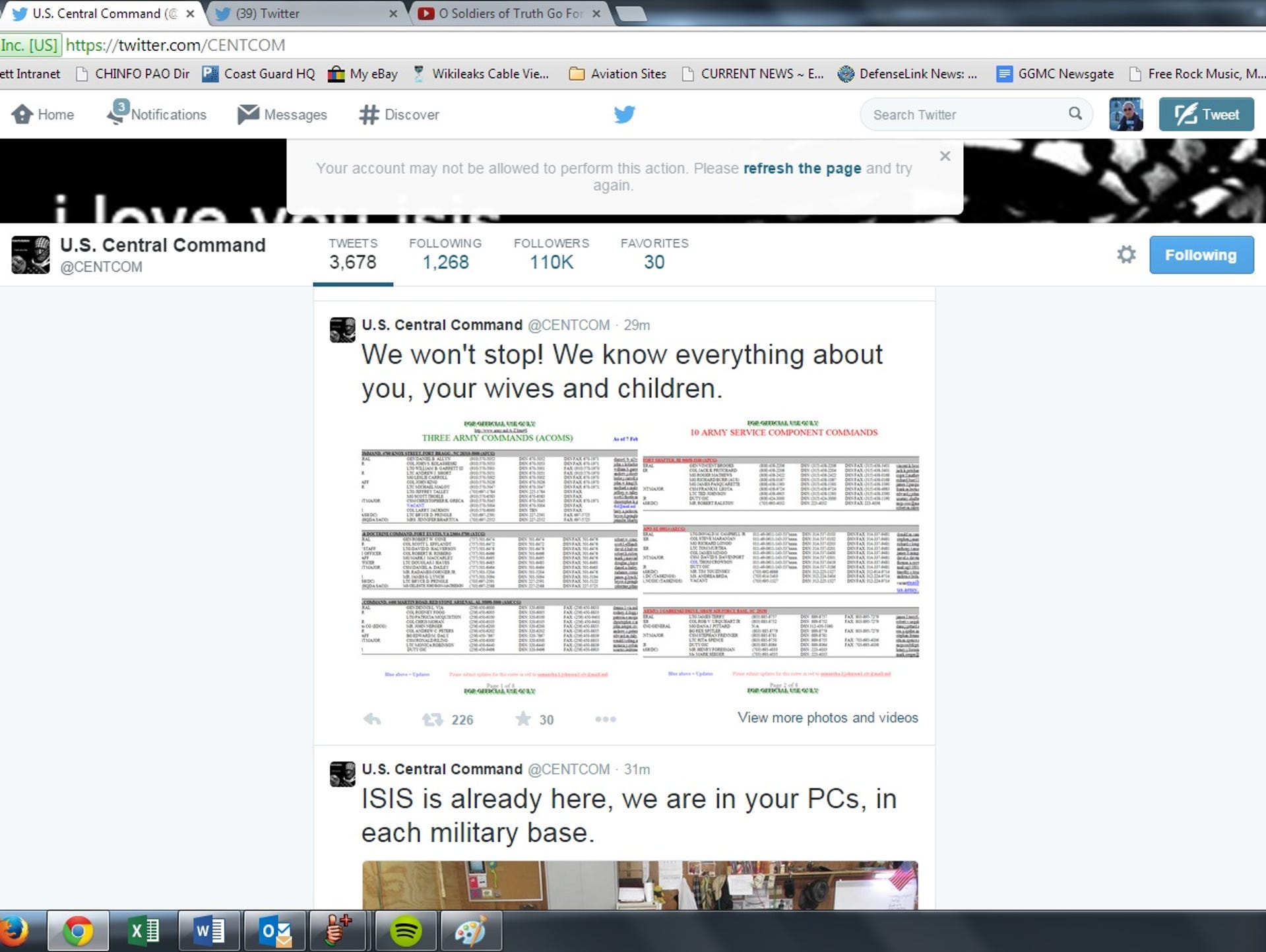
A later tweet, reading "We won't stop! We know everything about you, your wives and children" was accompanied by what appear to be personnel records, although the image quality was too low to be read.
In a statement to reporters, a the Pentagon indicated it was looking into the hack.
"We can confirm that the U.S. Central Command Twitter and YouTube accounts were compromised earlier today," a defense official said in an emailed statement. "We are taking appropriate measures to address the matter. I have no further information to provide at this time."
It took about 40 minutes for the account to be frozen and then taken down by Twitter. In the meantime, hackers also took control of CENTCOM's YouTube account, placing a number of pro-ISIS videos onto the account. Both accounts were suspended by 2 p.m. Eastern time.
While the event is publicly embarrassing for the Pentagon, the damage may be limited. It appears much, if not all, of the information posted online by the hackers is publicly available, including slides that appear to show wargaming scenarios for conflict with China and North Korea.
Ben Fitzgerald, director at the Center for a New American Security's Technology and National Security Program, wrote in an email to reporters that there is nothing at this time to indicate the hackers had access to classified materials.
"Releasing documents that were largely already in the public domain to look like 'leaks' to the uninitiated is a smart and inexpensive misinformation play and may seem credible to some given the bulk release of data by the likes of Snowden and Manning," Fitzgerald wrote, adding that the whole situation appears to be "more public relations stunt than major security breach."
"Hacking social media accounts for CENTCOM is no more difficult than hacking the social media account of a private citizen," he wrote, "and it would not be surprising to discover that CENTCOM's public affairs team had the same username and password for both accounts."
Matthew Aid, a cybersecurity expert, said in an interview Monday afternoon with sister publication MilitaryTimes that the hack is "embarrassing as all get-out for CENTCOM," but agreed there seems to be little true damage to the Pentagon.
"It looks like rather low-level classified documents," said Aid, who is the author of "Intel Wars: The Secret History of the Flight Against Terror."
Nevertheless, Aid said, "They came off a protected network. Regardless of the low level of sensitivity, the fact that it was done should scare the crap out of people.
"The question is: Where did they get this stuff? Did they hack CENTCOM and get this stuff or did they hack this material from some other site and just post it?" Aid said.
The hack does not necessarily reveal a flaw in CENTCOM's network security because protecting Twitter accounts is a responsibility that falls to Twitter, a California-based corporation.
But Aid noted that the lag time between the hack and CENTCOM's suspension of the account suggests the Florida-based command was not keeping close tabs on its social media account.
"They should have done a better job of monitoring their own site. According to what I was reading, this stuff was on their site for 35 or 45 minutes before it was suspended. Someone should have been on top of that," Aid said.
Fitzgerald noted that the timing of the hack, which coincided almost perfectly with a major speech by President Barack Obama on cybersecurity "should not be overlooked."
"The fact that this hack is inconsequential from a technical perspective is overshadowed by the easy and cheap win afforded to ISIS," he added. "Good username and password practices would likely have saved CENTCOM from this embarrassment."
But while outside analysts are downplaying the threat, at least one key member of Congress — House Committee on Homeland Security chairman Michael McCaul, R-TX — called the hack "severely disturbing."
"As I have repeatedly warned in the past, extremists are developing the capability to conduct cyberattacks against U.S. interests and those of our allies," McCaul said in a statement. "Assaults from cyber-jihadists will become more common unless the administration develops a strategy for appropriately responding to these cyberattacks—including those like the North Korea attack against Sony.
"Without laying out the rules of the game for offensive responses and having direct consequences, cyber threats and intrusions from our adversaries will continue and escalate."
The CyberCaliphate group has taken credit for a series of recent hacks, including a news website in New Mexico and a TV station in Maryland.
Late Monday, a Twitter account associated with the Anonymous activist collective tweeted out that the source of the hack was located in Maryland. It is unclear if that is real information or a joke, as the National Security Agency, a longtime Anonymous target, is based in that state:
Neither CENTCOM's Facebook or Pinterest accounts were impacted by the hack.
CENTCOM's Twitter, YouTube Feeds Hacked by ISIS Supporters

WASHINGTON — The Twitter and YouTube accounts of US Central Command were hacked Monday by people claiming to be sympathizers to the Islamic State militant group, commonly referred to as ISIS.
Just after noon East Coast time, the banner image on the @CENTCOM Twitter account shifted to an image of an ISIS fighter with "CyberCaliphate" written next to it. A link was tweeted to a message declaring "AMERICAN SOLDIERS, WE ARE COMING, WATCH YOUR BACK."
"While the US and its satellites kill our brothers in Syria, Iraq and Afghanistan we broke into your networks and personal devices and know everything about you," the statement read. "You'll see no mercy infidels. ISIS is already here, we are in your PCs, in each military base."
A later tweet, reading "We won't stop! We know everything about you, your wives and children" was accompanied by what appear to be personnel records, although the image quality was too low to be read.
In a statement to reporters, a the Pentagon indicated it was looking into the hack.
"We can confirm that the U.S. Central Command Twitter and YouTube accounts were compromised earlier today," a defense official said in an emailed statement. "We are taking appropriate measures to address the matter. I have no further information to provide at this time."
It took about 40 minutes for the account to be frozen and then taken down by Twitter. In the meantime, hackers also took control of CENTCOM's YouTube account, placing a number of pro-ISIS videos onto the account. Both accounts were suspended by 2 p.m. Eastern time.
While the event is publicly embarrassing for the Pentagon, the damage may be limited. It appears much, if not all, of the information posted online by the hackers is publicly available, including slides that appear to show wargaming scenarios for conflict with China and North Korea.
Ben Fitzgerald, director at the Center for a New American Security's Technology and National Security Program, wrote in an email to reporters that there is nothing at this time to indicate the hackers had access to classified materials.
"Releasing documents that were largely already in the public domain to look like 'leaks' to the uninitiated is a smart and inexpensive misinformation play and may seem credible to some given the bulk release of data by the likes of Snowden and Manning," Fitzgerald wrote, adding that the whole situation appears to be "more public relations stunt than major security breach."
"Hacking social media accounts for CENTCOM is no more difficult than hacking the social media account of a private citizen," he wrote, "and it would not be surprising to discover that CENTCOM's public affairs team had the same username and password for both accounts."
Matthew Aid, a cybersecurity expert, said in an interview Monday afternoon with sister publication MilitaryTimes that the hack is "embarrassing as all get-out for CENTCOM," but agreed there seems to be little true damage to the Pentagon.
"It looks like rather low-level classified documents," said Aid, who is the author of "Intel Wars: The Secret History of the Flight Against Terror."
Nevertheless, Aid said, "They came off a protected network. Regardless of the low level of sensitivity, the fact that it was done should scare the crap out of people.
"The question is: Where did they get this stuff? Did they hack CENTCOM and get this stuff or did they hack this material from some other site and just post it?" Aid said.
The hack does not necessarily reveal a flaw in CENTCOM's network security because protecting Twitter accounts is a responsibility that falls to Twitter, a California-based corporation.
But Aid noted that the lag time between the hack and CENTCOM's suspension of the account suggests the Florida-based command was not keeping close tabs on its social media account.
"They should have done a better job of monitoring their own site. According to what I was reading, this stuff was on their site for 35 or 45 minutes before it was suspended. Someone should have been on top of that," Aid said.
Fitzgerald noted that the timing of the hack, which coincided almost perfectly with a major speech by President Barack Obama on cybersecurity "should not be overlooked."
"The fact that this hack is inconsequential from a technical perspective is overshadowed by the easy and cheap win afforded to ISIS," he added. "Good username and password practices would likely have saved CENTCOM from this embarrassment."
But while outside analysts are downplaying the threat, at least one key member of Congress — House Committee on Homeland Security chairman Michael McCaul, R-TX — called the hack "severely disturbing."
"As I have repeatedly warned in the past, extremists are developing the capability to conduct cyberattacks against U.S. interests and those of our allies," McCaul said in a statement. "Assaults from cyber-jihadists will become more common unless the administration develops a strategy for appropriately responding to these cyberattacks—including those like the North Korea attack against Sony.
"Without laying out the rules of the game for offensive responses and having direct consequences, cyber threats and intrusions from our adversaries will continue and escalate."
The CyberCaliphate group has taken credit for a series of recent hacks, including a news website in New Mexico and a TV station in Maryland.
Late Monday, a Twitter account associated with the Anonymous activist collective tweeted out that the source of the hack was located in Maryland. It is unclear if that is real information or a joke, as the National Security Agency, a longtime Anonymous target, is based in that state:
Neither CENTCOM's Facebook or Pinterest accounts were impacted by the hack.
CENTCOM's Twitter, YouTube Feeds Hacked by ISIS Supporters
